Everything You Need to Know About IT Security Policy Compliance Audits
March 25, 2026

Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026

Strengthen your defenses with Vendor risk management services. Discover risks, compliance strategies, and lifecycle best practices now!
April 23, 2026

Discover top cloud management app tools for 2025. Optimize multi-cloud, boost security, cut costs & master hybrid environments like a pro!
April 17, 2026
March 25, 2026
IT security policy compliance audits are one of the most important tools a business has to protect itself from growing cyber threats — and to prove it's meeting the legal and regulatory standards that apply to its industry.
Here's a quick overview of what they involve:
WhatWhyHow OftenIndependent review of your IT controls, policies, and security systemsIdentify risks, close gaps, meet regulatory requirementsAt minimum annually; more often based on riskAssessed against frameworks like NIST, ISO 27001, HIPAA, PCI DSSAvoid fines, data breaches, and reputational damageContinuously monitored between formal auditsConducted by qualified, independent auditorsEnsure objectivity and accuracy of findingsInternal audits can happen more frequently
Cybercrime is getting more expensive every year — global costs are expected to hit $10.5 trillion annually by 2025. For mid-sized businesses especially, a single breach or compliance failure can be devastating. IT security policy compliance audits help you stay ahead of those risks by catching weaknesses before attackers — or regulators — do.
This guide walks you through everything: what these audits are, how they work, who should run them, and how to make the process as smooth as possible.
I'm Steve Payerle, President of Next Level Technologies, and I've spent over 15 years helping small and mid-sized businesses across Columbus, Ohio and Charleston, WV navigate IT security policy compliance audits as part of a broader managed IT and cybersecurity strategy. My team brings deep technical expertise and ongoing cybersecurity training to every engagement, so you can trust that what follows is grounded in real-world experience — not just theory.
Simple guide to it security policy compliance audits terms:
At its heart, an it security policy compliance audit is a comprehensive assessment of your organization’s information systems. It’s an independent examination where an expert looks at your IT controls, security systems, and risk mitigation policies to see if they actually match up with what you say you’re doing—and what the law requires you to do.
Think of it like a home inspection, but for your digital house. We aren’t just looking at the locks on the front door; we’re checking the wiring, the foundation, and making sure you’re following the local building codes. In it-compliance, those "codes" are frameworks like HIPAA or SOC 2.
The goal here is threefold:
By understanding-the-basics-of-it-compliance, we can move your business from a "reactive" state (fixing things after they break) to a "proactive" state (preventing them from breaking in the first place).
It’s easy to get these terms mixed up, but they serve different purposes. Here is how they break down:
FeatureIT Security AuditCompliance AuditPenetration TestingScopeBroad; looks at all IT infrastructure and policies.Narrow; focuses on specific regulatory rules (e.g., GDPR).Targeted; attempts to "hack" a specific system.ObjectiveEvaluate overall security posture.Verify adherence to legal/industry standards.Find known vulnerabilities and exploit them.OutcomeComprehensive report on security health.Pass/Fail or Attestation of compliance.List of specific technical flaws to patch.
While a penetration test is like testing if a specific window can be pried open, it-compliance-assessments are more about the governance review—checking if you have a policy that says "all windows must be locked" and then verifying that your team is actually following that policy every day.
When we perform these audits for our clients in Columbus or Charleston, we are looking for more than just a "check the box" result. The primary objectives include:
For those looking for a deep dive into how to structure these goals, you can learn more in this quick start guide from NIST, which provides a roadmap for using the Cybersecurity Framework (CSF). Meeting it-compliance-benchmarks isn't just about security; it's about building a more resilient, professional organization.
Not every audit is the same because not every business is governed by the same rules. Depending on your industry—whether you're a doctor's office in Charleston or a manufacturing plant in Columbus—you’ll be measured against different standards.
Understanding IT compliance requirements for different industries is the first step in choosing the right path. From there, you can pursue specific it-compliance-certifications to prove your commitment to security to your partners and clients.
Audits can be categorized by who performs them and what they focus on:

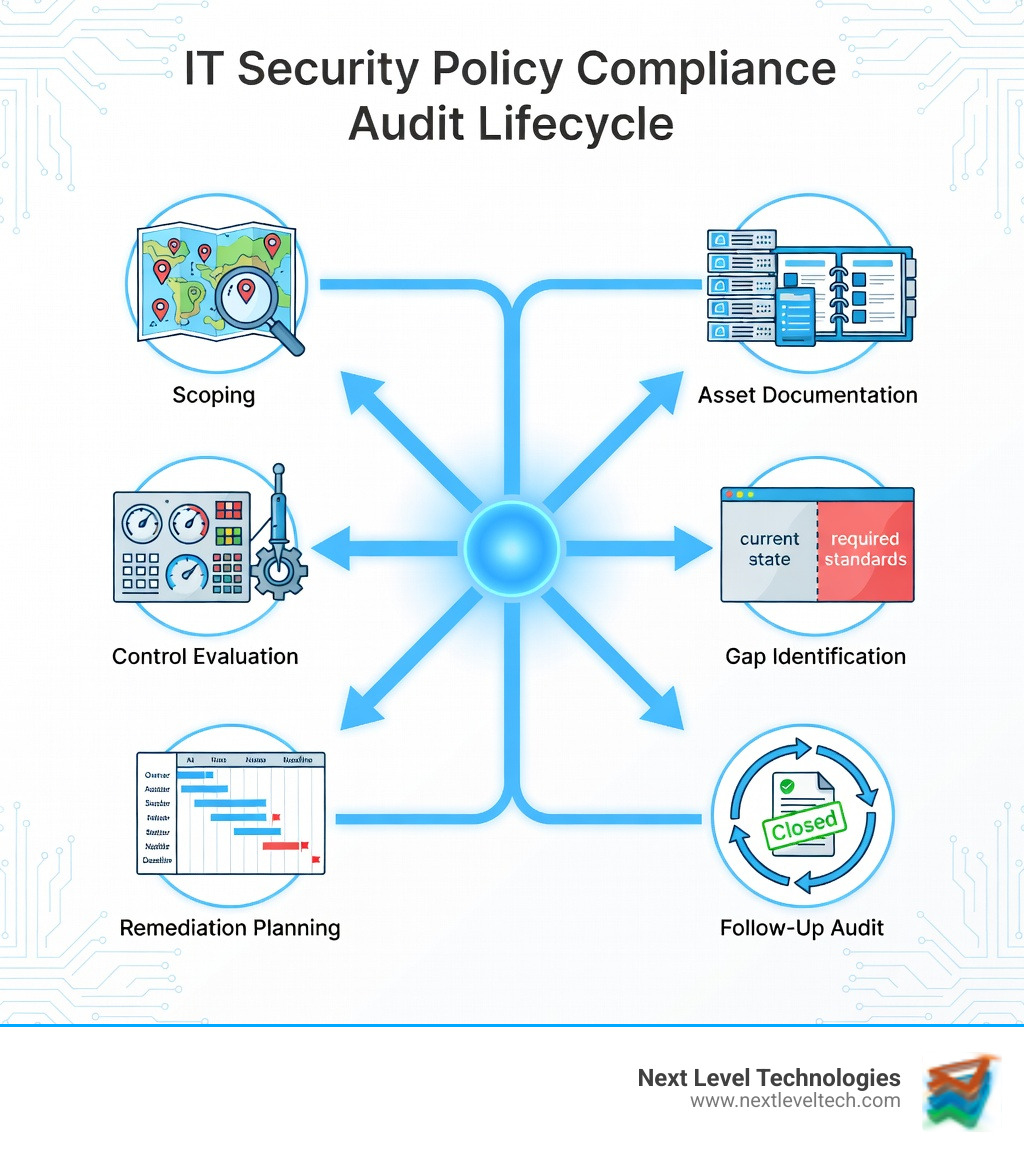
Conducting an audit doesn't have to be a nightmare if you follow a structured process. At Next Level Technologies, we break it down into manageable chunks:
You can't protect what you don't know you have. We start by identifying every server, laptop, and piece of software your company uses. This is where it-compliance-monitoring begins—setting a baseline of all your assets.
We compare your current setup against your chosen framework (like NIST or HIPAA). Where are you falling short? This compliance-gap-analysis is the most critical part of the audit, as it highlights exactly where your vulnerabilities lie.
Once we find the gaps, we create a plan to fix them. This might include updating your soc2-change-management procedures or implementing new technical controls.
Remediation isn't "one and done." We perform follow-up checks to make sure the fixes actually worked and that no new holes were poked in your security during the process.
If you're just starting out, here is a foundational checklist to get your house in order. You can also get a FREE DOWNLOAD › IT Compliance Audit Checklist: A Practical Guide for Beginners for a more detailed version.
By demystifying-it-compliance-beginners-guide-for-small-business-success, we help you see that these steps are just good business hygiene.
The biggest hurdle in it security policy compliance audits is often the manual workload. Digging through spreadsheets and old emails to find "proof" of security is a waste of your time.
Thankfully, technology is catching up. Data published in the International Journal of Research Publication and Reviews shows that AI-enhanced cybersecurity methods can improve threat detection speeds from weeks or months to just minutes or hours. Accuracy also jumps from around 70% to over 90%.
We use cybersecurity-audit-and-compliance-solutions that automate the "boring stuff." Tools like real-time monitoring and automated evidence collection allow our cybersecurity-compliance-services to be more accurate and less intrusive for your staff.
Independence is the key word here. You wouldn't want to grade your own homework, right? An auditor needs to be objective.
A qualified auditor should have:
This is how-managed-it-services-help-small-businesses-with-regulatory-compliance. By bringing in an outside team with extensive cybersecurity training, you get a fresh set of eyes that can spot things your internal team might miss because "that's just how we've always done it."
At a bare minimum, you should conduct a full audit once a year. However, if you are in a high-risk industry like finance or healthcare, or if your business is growing rapidly, you might need them quarterly. The Computer Security Resource Center suggests that continuous monitoring is the best way to stay safe between formal audit periods.
An audit shouldn't just result in a report that sits on a shelf. It should lead to a Management Action Plan. This includes updating policies that are no longer working, launching new training initiatives, and fixing technical gaps. This cycle of improvement is what keeps your business resilient over the long haul.
In the end, it security policy compliance audits aren't just about avoiding trouble with regulators—they're about building a foundation of trust with your customers and ensuring your business can survive in an increasingly dangerous digital world.
Whether you are based in Columbus, OH, or Charleston, WV, Next Level Technologies is here to help. Our team’s technical expertise and constant cybersecurity training mean we don't just point out problems—we provide the solutions to fix them. We specialize in helping mid-sized businesses and overlooked industries navigate these complex requirements with ease.
Ready to take your security to the next level? Contact us today for Managed IT Services and IT Support that keep you compliant, secure, and ready for whatever comes next.
Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026
Strengthen your defenses with Vendor risk management services. Discover risks, compliance strategies, and lifecycle best practices now!
April 23, 2026
Next Level Technologies was founded to provide a better alternative to traditional computer repair and ‘break/fix’ services. Headquartered in Columbus, Ohio since 2009, the company has been helping it’s clients transform their organizations through smart, efficient, and surprisingly cost-effective IT solutions.
