Why Your Third-Party Risk Strategy is Leaking
April 23, 2026

Master the basics of computer hardware and networking with this in-depth guide covering components, systems, and troubleshooting.
June 6, 2026

Discover how IT server management services boost uptime, security, and compliance for businesses in Columbus, Ohio and Charleston, West Virginia.
June 2, 2026

Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026
April 23, 2026
Vendor risk management services are structured solutions that help organizations identify, assess, and reduce the risks that come from working with outside vendors, suppliers, and third-party partners.
Here is a quick breakdown of what they cover:
| What It Does | Why It Matters |
|---|---|
| Screens vendors before onboarding | Stops risky partners from entering your ecosystem |
| Monitors vendors continuously | Catches new threats as they emerge |
| Tracks compliance requirements | Keeps you aligned with GDPR, HIPAA, NIST, and more |
| Manages the full vendor lifecycle | Covers selection through offboarding |
| Automates risk scoring and alerts | Reduces manual work and human error |
Every time you hand a vendor access to your systems, data, or network, you are taking on risk. Most businesses know this. But most are not managing it well.
The numbers are striking. According to research by the Ponemon Institute, 66% of organizations have experienced a data breach caused by a vendor security failure. And yet only 34% of those same organizations felt confident their vendors would even report a breach promptly.
Think about that for a moment. Two out of three companies have already been burned through a third party — and most of those companies had little warning it was coming.
It is not just IT teams losing sleep over this. A striking 94% of CISOs have expressed serious concern about third-party cybersecurity threats. The risk is real, it is growing, and for many mid-sized businesses, the strategy to address it has serious gaps.
I'm Steve Payerle, President of Next Level Technologies, and I have spent years helping businesses across Columbus, Ohio and Charleston, WV close exactly these kinds of gaps through managed IT and cybersecurity services — including vendor risk management services that protect organizations from threats they often do not see coming until it is too late.

Vendor risk management services word roundup:
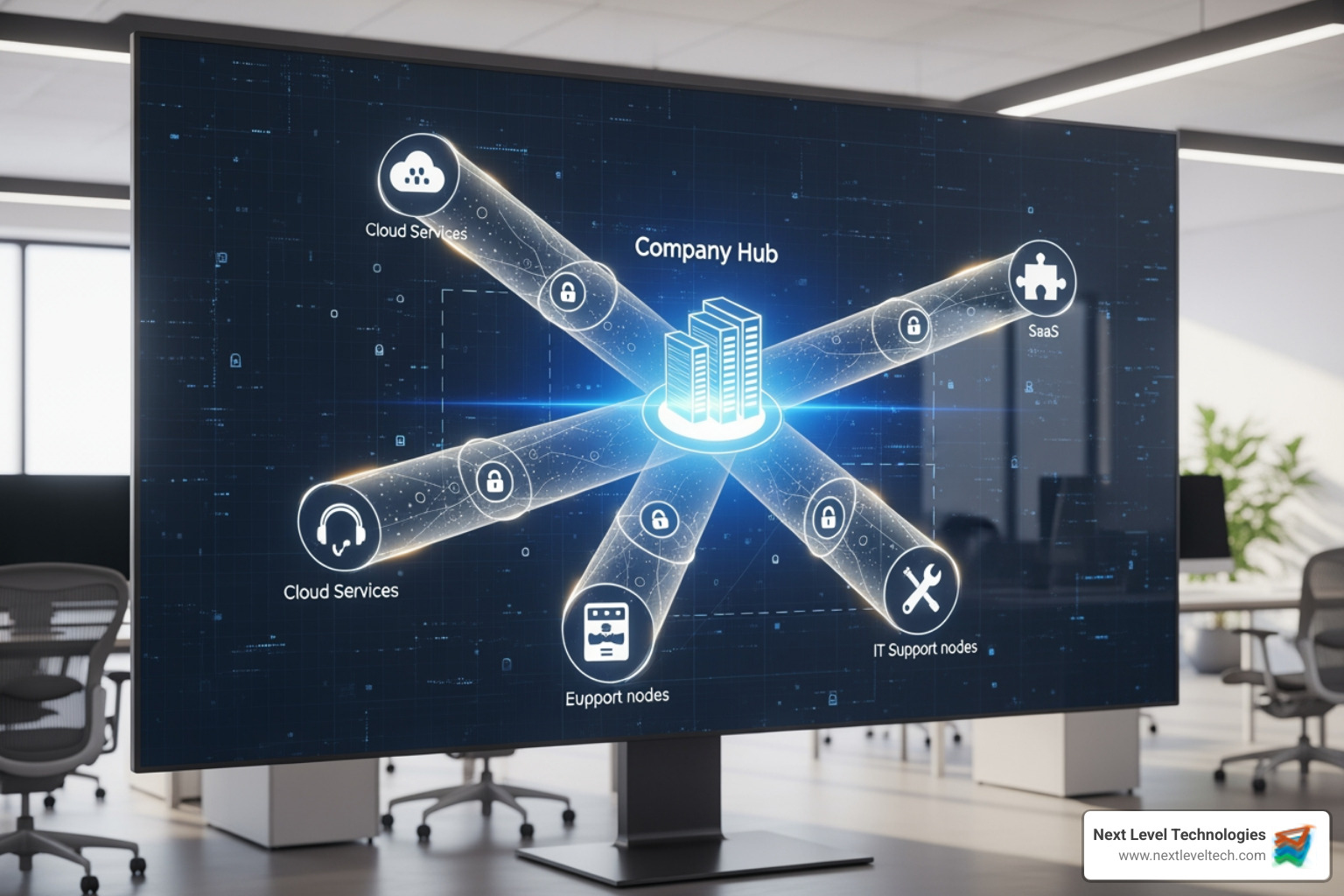
In the modern business landscape, no company is an island. Whether we are talking about a law firm in Columbus or a manufacturing plant in Charleston, we all rely on a massive web of third-party providers. You use cloud hosting for your data, SaaS platforms for your payroll, and external IT teams for your support. This interconnectedness is great for efficiency, but it creates a "leaky" perimeter.
When we talk about vendor risk management services, we aren't just talking about a one-time background check. We are talking about a comprehensive discipline that ensures your partners are as secure as you are. If a vendor has weak security protocols, they aren't just a risk to themselves; they are a direct gateway into your network.
This is why it-vendor-risk-management-solutions have become a cornerstone of operational resilience. A strong VRM program allows us to:
To do this effectively, many organizations align their programs with the NIST Cybersecurity Framework. This framework provides a high-level "language" for managing risk, helping us identify where our vendors sit within our broader security posture. By treating vendor risk as a core business function rather than an IT afterthought, we stop the "leaks" before they turn into floods.
Not all risks are created equal. When we evaluate vendors for our clients, we look through five specific lenses. If you only focus on one—usually cybersecurity—you are leaving the back door wide open for the other four.
This is the "big one." It involves the risk of data breaches, malware infections, or ransomware attacks originating from a vendor. Because cyber risk can change in an instant (a new zero-day vulnerability doesn't wait for your annual audit), it requires persistent, real-time monitoring.
Are your vendors following the law? If you are a healthcare provider in West Virginia, your vendors must comply with HIPAA security guidance. If you serve customers in the EU, GDPR data protection standards are non-negotiable. If a vendor fails a regulatory audit, the legal and financial responsibility often falls back on you.
What happens if your primary software provider goes bankrupt tomorrow? Financial risk assessments involve checking a vendor’s credit history and fiscal health. A vendor in financial trouble is likely to cut corners on security and support, or worse, disappear entirely, leaving your operations in the lurch.
This is the risk that a vendor fails to deliver the promised service. Think of a supply chain delay or a cloud outage. If your business can't function because a third party is down, you have an operational risk problem.
We live in an age of "guilt by association." If your vendor is caught using unethical labor practices or is involved in a high-profile scandal, your brand takes the hit. Public perception doesn't care that they were "just a contractor."
Managing a vendor is a lot like a long-term relationship. There’s the "getting to know you" phase, the "moving in" phase, the "daily life" phase, and sometimes, the "breakup." Vendor risk management services cover every single one of these steps.
Before you sign a contract, you need to know what you are getting into. This starts with identifying the vendor's criticality. Will they have access to PII (Personally Identifiable Information)? Will they be integrated into your network?
This is the deep dive. We don't just take a vendor's word for it. We look for certifications like ISO 27001 security standards or SOC 2 Type II reports. This phase is about verifying that their "security" isn't just a marketing slogan.
Once a vendor passes the test, the risk requirements must be baked into the contract. This includes Service Level Agreements (SLAs), right-to-audit clauses, and mandatory breach notification timelines. Knowing how to manage IT vendors effectively means having the legal teeth to hold them accountable.
This is where most strategies fail. A vendor who was secure two years ago might not be secure today. Continuous monitoring involves tracking security ratings, news feeds for lawsuits, and periodic re-assessments. It is a "trust but verify" model.
When the relationship ends, the risk doesn't automatically vanish. You must ensure that all data is returned or destroyed, and all system access is revoked. A "ghost" account for a former vendor is a massive security hole.
To move from a reactive "firefighting" mode to a proactive stance, you need a structured plan. At Next Level Technologies, we emphasize that a good strategy is built on data, not guesswork.
First, you must define your risk appetite. How much risk is your organization willing to accept to achieve its goals? A tech startup might have a higher appetite for risk than a local government agency in Charleston. Once that’s established, you can use standardized questionnaires (like the SIG or CAIQ) to gather consistent data across your vendor pool.
However, manual spreadsheets are the enemy of scale. Workflow automation is essential. By automating the collection of evidence and the scoring of risks, you free up your team to focus on the high-risk outliers. This is where it-vendor-management-analyst roles come in—they interpret the data and drive remediation efforts.
If you are looking for a VRM platform or service, here are the non-negotiables:
Many small business owners in Ohio and West Virginia think, "I'm too small to be a target." The reality is the opposite. Small businesses are often used as "stepping stones" to reach larger targets in a supply chain attack.
Small businesses face unique challenges:
This is why scalable, managed vendor risk management services are so vital. They provide the expertise and tools of an enterprise-level security team at a price point that makes sense for a growing business. Staying updated with CISA cybersecurity advisories is a great first step for any SMB looking to understand the current threat landscape.
Compliance is often the "stick" that drives businesses toward better risk management. Depending on your industry and location, you may be subject to a variety of overlapping standards.
| Regulation | Primary Focus | Who It Affects |
|---|---|---|
| GDPR | Data Privacy & Protection | Any business with EU citizen data |
| HIPAA | Patient Data Security | Healthcare providers and their vendors |
| CMMC | Defense Industrial Base Security | DoD contractors and suppliers |
| NIST 800-171 | Protection of CUI | Non-federal systems handling govt data |
One of the biggest shifts in recent years is the focus on Fourth-party risk. This is the risk posed by your vendor's vendors. If your cloud provider uses a sub-contractor for data storage, you are indirectly reliant on that sub-contractor's security. Modern VRM programs must look "down the chain" to ensure total visibility.
We also see international standards influencing local business. For instance, the UK Modern Slavery Act and the APRA CPS 234 standards for financial services highlight a global trend: regulators are holding companies strictly accountable for the actions of their third parties.
Don't panic, but act fast. Your first step should be to activate your Incident Response Plan. You need to determine what data was accessed, whether the vendor has contained the threat, and what your legal notification obligations are. Collaboration is key—work with the vendor to understand the root cause and ensure it doesn't happen again.
AI is a game-changer for analyzing massive amounts of data. It can scan thousands of pages of vendor SOC reports to find "gotchas" in seconds. Automation handles the "busy work" of sending out questionnaires and following up on expired certifications, allowing your human experts to focus on complex decision-making.
Beyond just "not getting hacked," a strong program leads to:
At the end of the day, your security is only as strong as the weakest link in your vendor chain. If you aren't actively managing those links, your strategy isn't just leaking—it’s wide open.
At Next Level Technologies, we specialize in helping businesses in Columbus, Ohio and Charleston, WV navigate these complexities. Our team doesn't just "check boxes." We bring extensive technical experience and hold advanced certifications like CISSP, CRISC, and CCNA. We undergo continuous, extensive cybersecurity training to stay ahead of the same threats that are targeting your vendors.
Whether you need a full suite of vendor risk management services or a partner to handle your broader Managed IT Services and IT Support, we are here to help you build a resilient, secure, and leak-proof business.
Let’s stop the leaks together. Give us a call at our Columbus or Charleston offices today, and let's get your third-party risk under control.
Master the basics of computer hardware and networking with this in-depth guide covering components, systems, and troubleshooting.
June 6, 2026
Discover how IT server management services boost uptime, security, and compliance for businesses in Columbus, Ohio and Charleston, West Virginia.
June 2, 2026
Next Level Technologies was founded to provide a better alternative to traditional computer repair and ‘break/fix’ services. Headquartered in Columbus, Ohio since 2009, the company has been helping it’s clients transform their organizations through smart, efficient, and surprisingly cost-effective IT solutions.
