The Best Security Compliance Services for Beginners
February 25, 2026

Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026

Strengthen your defenses with Vendor risk management services. Discover risks, compliance strategies, and lifecycle best practices now!
April 23, 2026

Discover top cloud management app tools for 2025. Optimize multi-cloud, boost security, cut costs & master hybrid environments like a pro!
April 17, 2026
February 25, 2026
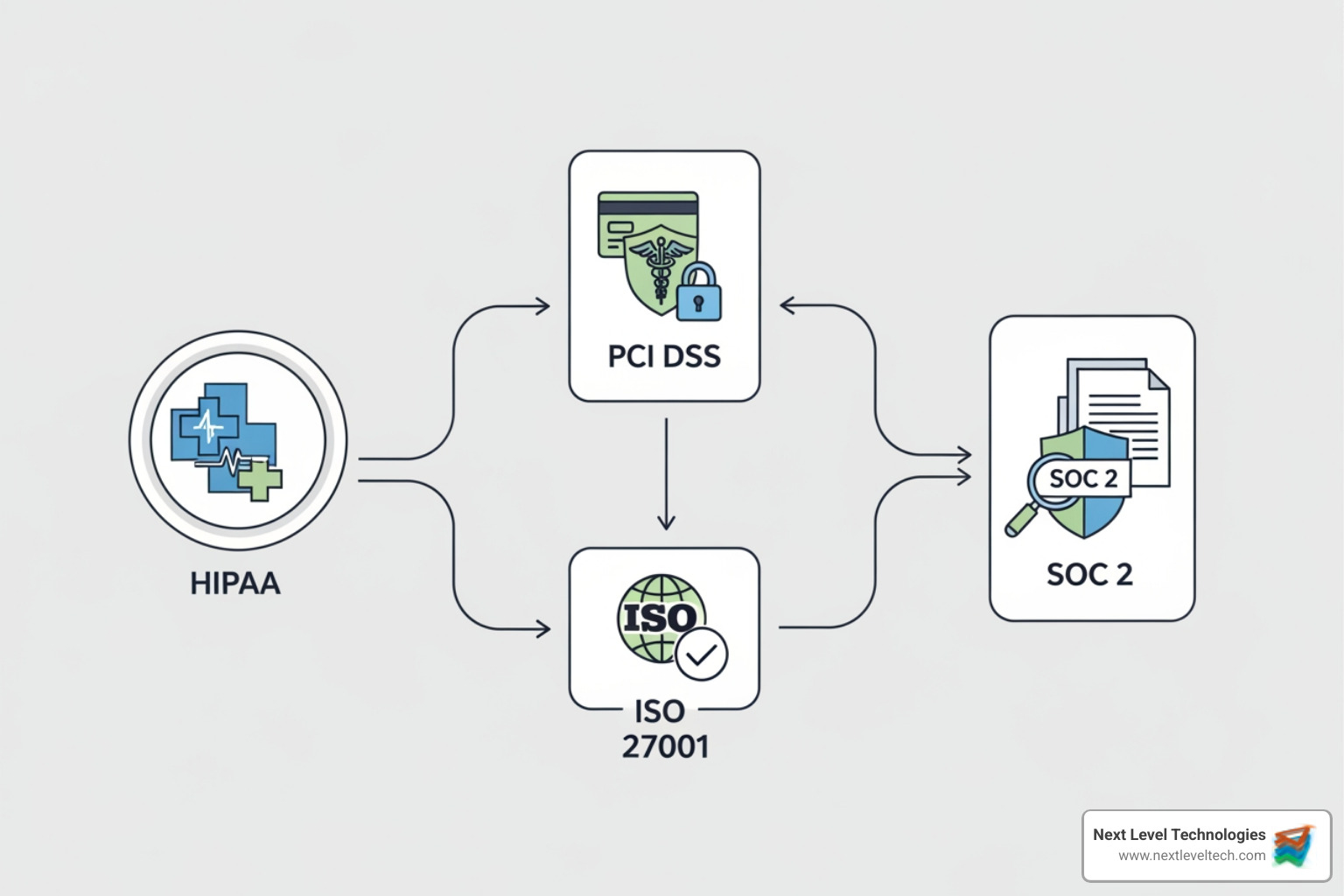
Security Compliance Services help organizations meet regulatory requirements and protect their data by implementing industry-standard frameworks, conducting assessments, and ensuring ongoing adherence to cybersecurity standards like NIST, HIPAA, PCI DSS, ISO 27001, and SOC 2.
What Security Compliance Services Include:
If you're running a mid-sized business, cybersecurity compliance probably feels overwhelming. You're not alone. Cybersecurity threats are on the rise for organizations of all sizes - and in nearly every industry. At the same time, there's building pressure for companies to prove they have effective controls in place.
Cybersecurity compliance is the act of ensuring your company and employees satisfy the ethical practices, regulations, standards, and laws that apply to information and technology. It manifests as a program of controls aimed at protecting the integrity, accessibility, and confidentiality of your organization's data.
Why does this matter? Compliance violations can result in significant legal ramifications, often involving hefty fines. But beyond avoiding penalties, implementing proper security compliance protects your business from data breaches, builds customer trust, and gives you a competitive edge.
The good news is you don't have to steer this alone. Security compliance services provide expert guidance throughout the entire process, helping you implement the right frameworks, pass audits, and maintain ongoing compliance - all while you focus on running your business.
I'm Steve Payerle, President of Next Level Technologies, where we've helped businesses across Ohio and West Virginia steer complex compliance requirements since 2009. Our team's extensive cybersecurity training and technical experience in Security Compliance Services enables us to transform overwhelming regulatory requirements into manageable, strategic IT solutions for our clients.

Security Compliance Services terminology:
In today's digital landscape, where data breaches are a constant threat and regulatory scrutiny is at an all-time high, understanding the foundations of security compliance is not just good practice—it's essential for survival. For businesses in Columbus, OH, Charleston, WV, and beyond, navigating this complex terrain can feel daunting.
Why is compliance so critical? Simply put, it's about mitigating risk, building customer trust, and safeguarding your business's future. Cybersecurity compliance is more than just a tick-box exercise; it's a proactive defense against the changing threat landscape. By adhering to established standards, we help protect your sensitive data from unauthorized access, loss, or corruption. This, in turn, fosters confidence among your customers and partners, assuring them that their information is in safe hands.
The consequences of non-compliance are severe and far-reaching. Compliance violations can, especially in the case of government mandates, result in significant legal ramifications, often involving hefty fines that can cripple a business. Beyond financial penalties, non-compliance can lead to severe reputational damage, eroding customer trust and potentially impacting your ability to operate. Legal action from affected parties is also a very real possibility. There's building pressure for companies to prove they have effective controls in place, and failing to do so can have disastrous consequences.
To help you gain a clearer understanding of this crucial topic, we've put together a guide on Demystifying IT Compliance: Beginner's Guide for Small Business Success. You can also review widely recognized standards like Information Security Management at ISO/IEC 27001 to see how global best practices are structured.
A compliance framework is essentially a structured set of guidelines, policies, and procedures designed to help organizations manage their cybersecurity risks and adhere to regulatory requirements. Think of it as a blueprint for building a secure and compliant IT environment. Implementing a cybersecurity framework associated with official standards is one way to ensure your organization's compliance.
Here are some of the most common and widely recognized industry-standard cybersecurity compliance frameworks:
Understanding which frameworks apply to your business can be complex. That's why we've put together insights on Understanding IT Compliance Requirements for Different Industries.
Adopting a recognized cybersecurity framework offers a wealth of benefits that extend far beyond simply avoiding penalties. It provides a structured approach to security, helping your organization systematically identify, assess, and manage risks.
Here's why implementing a cybersecurity framework is a game-changer:
Navigating the intricate world of cybersecurity regulations and standards can feel like trying to solve a Rubik's Cube blindfolded. This is where professional Security Compliance Services truly shine. For businesses in Columbus, OH, and Charleston, WV, partnering with experts like us means gaining a clear vision and a steady hand to guide you through these complexities.

Our services provide expert guidance, bridging any skills gaps your internal team might have, and ensuring you meet all necessary regulatory requirements. We help mitigate risks by identifying vulnerabilities and implementing robust security measures custom to your specific needs. Think of us as your cybersecurity co-pilot, helping you steer clear of turbulence. For a broader understanding of how we help businesses, explore our Cybersecurity for Business Complete Guide. We also detail how Managed IT Services Help Small Businesses with Regulatory Compliance.
A compliance assessment is a fundamental step in achieving and maintaining cybersecurity compliance. It's not just an audit; it's a diagnostic tool. As the research states, "a compliance assessment is a process your organization must go through to certify that implemented policies, controls, and security compliance solutions meet requirements." This process verifies that your security practices align with relevant regulations and industry standards.
The typical steps involved in a compliance assessment include:
Compliance assessments can be either internal, conducted by your own team, or external, performed by independent third-party experts. While internal assessments are valuable for ongoing monitoring, external audits provide an unbiased, authoritative validation of your compliance posture. To learn more about this crucial process, check out our insights on IT Compliance Assessments.
An effective cybersecurity compliance program is a multi-faceted endeavor, built upon several interconnected components designed to protect your organization's digital assets. These components work together to create a robust defense against threats and ensure adherence to regulatory mandates.
Once you've implemented a robust cybersecurity program, the next step is often proving its effectiveness through various compliance reports and audits. These documents are vital for demonstrating your adherence to standards, building trust with partners, and satisfying regulatory bodies.
Understanding these audit reports is key. They serve as formal attestations of your organization's security posture and control environment. Whether you're trying to secure a new client, satisfy an existing one, or meet a regulatory mandate, these reports provide the necessary evidence. We offer comprehensive Cybersecurity Audit and Compliance Solutions to help you steer this landscape.
Among the most common and impactful compliance reports are SOC (System and Organization Controls) reports. As our research notes, "SOC (System and Organization Controls) is a suite of reports produced by an audit of an organization’s internal controls." These reports are critical for service organizations that handle customer data or impact their clients' financial reporting. Audits for SOC reports are typically conducted by Certified Public Accountants (CPAs) accredited by the American Institute of Certified Public Accountants (AICPA).
There are three main types of SOC reports:
Preparing for and successfully completing a compliance audit, especially for something as rigorous as a SOC 2 Type 2, is a complex undertaking. It requires deep expertise, meticulous documentation, and a thorough understanding of the audit process. This is precisely why your business needs dedicated Security Compliance Services.
The complexity of audit preparation can quickly overwhelm internal teams, diverting valuable resources from core business operations. Our experts in Columbus, OH, and Charleston, WV, possess extensive cybersecurity training and technical experience, enabling us to steer these complexities on your behalf. We assist with everything from initial readiness assessments and gap analysis to developing necessary policies and procedures, gathering evidence, and liaising with auditors.
By partnering with us, you ensure successful outcomes for your audits, providing the peace of mind that your critical information is in good hands. Our highly trained staff understands the nuances of various frameworks and audit requirements, helping you avoid common pitfalls and streamline the entire process. This not only saves you time and resources but also helps in maintaining continuous compliance, which is essential in today's dynamic regulatory environment.
Selecting the right partner for your Security Compliance Services is a critical decision that can significantly impact your business's security posture and regulatory standing. It's not just about finding a vendor; it's about establishing a trusted partnership. For businesses in Columbus, OH, and Charleston, WV, finding a local expert with a deep understanding of your unique challenges is invaluable.
When assessing your needs, consider your industry-specific regulations (e.g., HIPAA for healthcare, PCI DSS for e-commerce) and the size and nature of your business. A small business might have different compliance needs than a large enterprise, but the importance of data protection remains universal.
When evaluating potential providers, look for proven experience and relevant certifications. Do they have a track record of successful compliance projects? Do their staff hold industry-recognized cybersecurity certifications? At Next Level Technologies, our team's comprehensive cybersecurity training and technical experience ensure we're not just service providers, but true partners in your compliance journey. We pride ourselves on our deep expertise in managed IT and compliance for diverse industries, with highly trained staff ready to support your needs in both Columbus, OH, and Charleston, WV. For more insights on this, refer to our page on IT Compliance Certifications.
Beyond general experience, several key factors should guide your decision when choosing Security Compliance Services:
For a deeper understanding of integrated solutions, explore our Compliance IT Solutions.
We often encounter similar questions from businesses just starting their compliance journey. Let's address some of the most common ones to provide further clarity.
This is a question we hear frequently, and the answer is unequivocal: cyber threats target all sizes. Small businesses are often seen as easier targets by cybercriminals because they may have fewer resources dedicated to security. Your data, regardless of your company's size, is valuable—to you, your customers, and unfortunately, to hackers. Regulatory mandates, such as those for protecting credit card data (PCI DSS) or customer privacy, often apply broadly, not just to large corporations. Moreover, achieving compliance helps build trust with your clients, which is invaluable for any business, big or small.
It's easy to confuse these two, but they represent different aspects of data protection. Think of it this way:
While it's technically possible to attempt to handle compliance entirely on your own, it's often a challenging and resource-intensive endeavor. It requires deep expertise in cybersecurity, regulatory frameworks, and audit processes, as well as significant time and dedicated resources. Many small to mid-sized businesses find it difficult to maintain this level of internal expertise while also focusing on their core operations.
Security Compliance Services provide efficiency and assurance. Our expert teams, particularly our technically experienced staff in Columbus, OH, and Charleston, WV, possess the specialized knowledge and tools to steer complex regulatory landscapes, perform thorough assessments, implement effective controls, and prepare you for audits. Partnering with professionals helps you avoid common pitfalls, reduces the burden on your internal team, and ultimately provides greater confidence in your compliance posture.
We hope this guide has demystified Security Compliance Services for you. What we want you to take away most is that compliance is not a burden, but a journey—a continuous process that strengthens your organization, protects your assets, and improves your reputation. A proactive approach to cybersecurity compliance is not just about meeting minimum requirements; it's about building a resilient, trustworthy business in an increasingly digital world.
The landscape of cybersecurity threats and regulatory mandates is constantly evolving. Attempting to steer it alone can be overwhelming and leave your business exposed to significant risks. By partnering with experts who possess extensive cybersecurity training and technical experience, like our team at Next Level Technologies in Columbus, OH, and Charleston, WV, you gain a strategic advantage. We translate complex requirements into actionable steps, ensuring your business is not just compliant, but truly secure.
Don't wait for a breach or a regulatory fine to prioritize your cybersecurity compliance. Take the next step towards a secure and compliant future.
Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026
Strengthen your defenses with Vendor risk management services. Discover risks, compliance strategies, and lifecycle best practices now!
April 23, 2026
Next Level Technologies was founded to provide a better alternative to traditional computer repair and ‘break/fix’ services. Headquartered in Columbus, Ohio since 2009, the company has been helping it’s clients transform their organizations through smart, efficient, and surprisingly cost-effective IT solutions.
