Beyond the Firewall: Unlocking Robust IT Security for Your Business
August 27, 2025

Discover how IT server management services boost uptime, security, and compliance for businesses in Columbus, Ohio and Charleston, West Virginia.
June 2, 2026

Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026

Strengthen your defenses with Vendor risk management services. Discover risks, compliance strategies, and lifecycle best practices now!
April 23, 2026
August 27, 2025
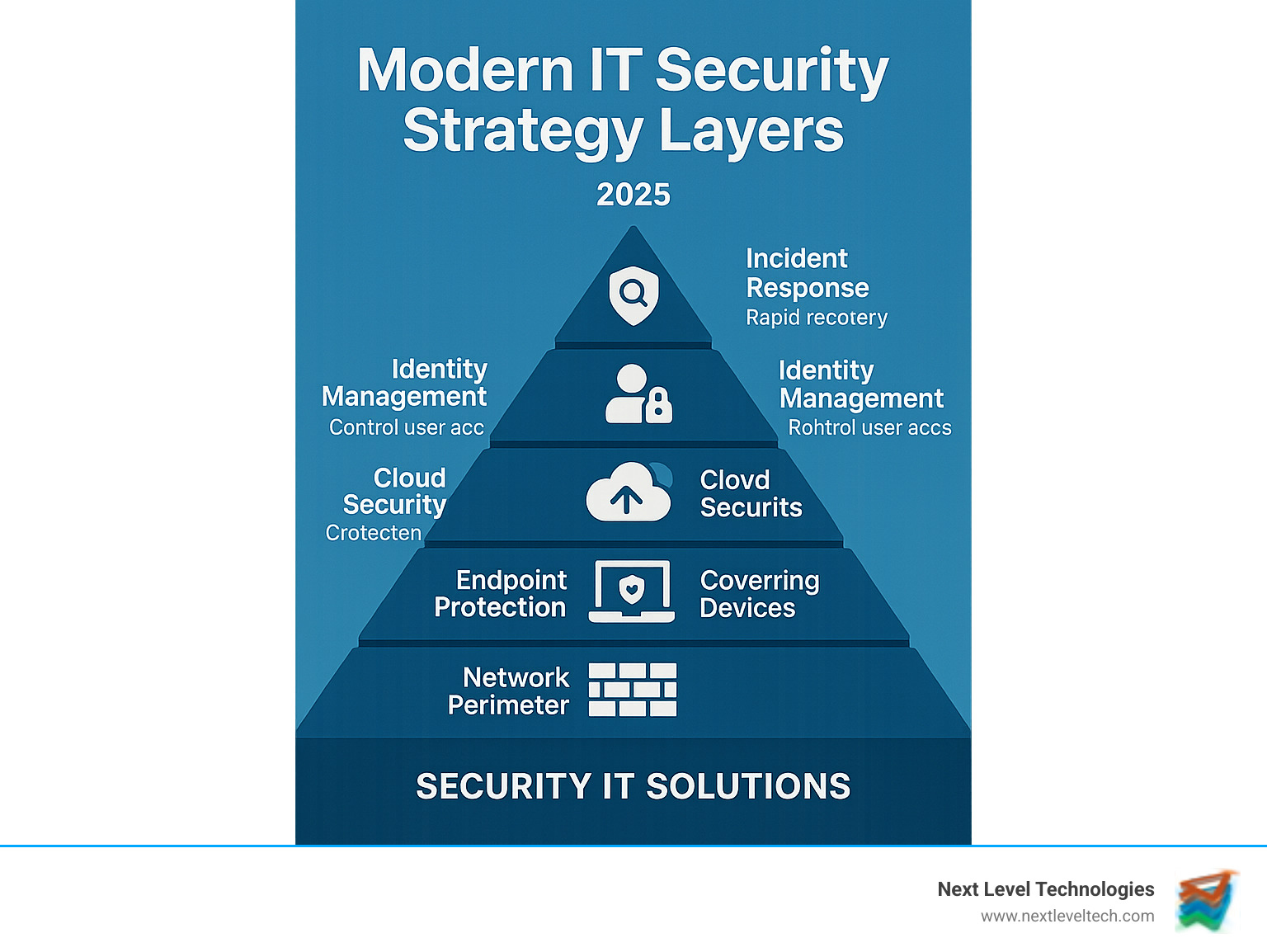
Security it solutions are comprehensive technology systems that protect businesses from cyber threats through multiple layers of defense, including firewalls, endpoint protection, threat detection, and incident response capabilities.
Key components of effective security IT solutions include:
The cybersecurity landscape has changed dramatically. Today's cyber threats are more sophisticated than ever, with AI-powered attacks that can succeed in minutes. The average cost of a data breach reached $4.45 million in 2023, while ransomware attacks continue to surge.
For many businesses, outdated security measures leave critical gaps. A simple firewall and basic antivirus software are no longer enough to defend against modern threats like zero-day exploits, advanced persistent threats, and AI-improved social engineering.
Modern security IT solutions offer layered protection that adapts to evolving threats while remaining cost-effective. These systems work together to create a robust defense that protects your data, maintains compliance, and ensures business continuity.
As Steve Payerle, President of Next Level Technologies, I've spent over 15 years helping businesses in Columbus, Ohio and Charleston, WV implement comprehensive security it solutions. My team's extensive cybersecurity training and technical experience have shown us that proactive, multi-layered security is essential for business resilience.
Security it solutions terms to know:
A strong defense requires layering different security IT solutions so they work together seamlessly, creating an impenetrable fortress for your data and business operations. At Next Level Technologies, our extensive cybersecurity training has shown us that a comprehensive strategy is built on these fundamental pillars:
For a deeper dive, explore our insights on Advanced Threat Protection Solutions and Cloud Security Best Practices.
Several key technologies are the workhorses of any strong security IT solution:
This quick comparison shows how comprehensive security IT solutions fit together:
| Solution Type | Primary Function | Key Advantages | When to Use |
|---|---|---|---|
| SIEM (Security Information and Event Management) | Centralized logging, correlation, and analysis of security events from across the IT environment. | Provides a holistic view of security posture, aids compliance, supports threat hunting. | For large organizations needing deep security analytics, compliance reporting, and long-term log retention. Microsoft Sentinel is a prime example, offering a unified data lake and dynamic threat intelligence. |
| XDR (Extended Detection and Response) | Integrates and correlates security data across multiple domains (endpoints, network, cloud, identity, email) to provide broader visibility and faster, more effective threat detection and response. | Reduces alert fatigue, automates response, offers superior threat context. | For organizations seeking to unify their security operations, improve incident response, and gain comprehensive visibility across their IT ecosystem. Microsoft Defender is a strong player in this space. |
| Endpoint Security | Protects individual devices (laptops, servers, mobile phones) from malware, ransomware, and unauthorized access. | Essential first line of defense, provides real-time protection, often includes features like device control and host firewall management. | For every organization, regardless of size, to protect the devices users interact with daily. CrowdStrike Falcon and Dell's Endpoint Security are leading solutions here. |
As businesses adopt hybrid and multi-cloud environments, securing these distributed infrastructures is a top priority. Our team at Next Level Technologies, with our deep technical experience, helps clients in Columbus, Ohio, and Charleston, WV steer this complexity by focusing on key areas:
For more on protecting cloud assets, see our articles on Cloud IT Security and Cloud Enterprise Security Providers.

In cybersecurity, reacting to threats means you've already lost. The best security IT solutions are proactive, preventing attacks from succeeding in the first place. This proactive mindset is key to digital security.
Our team's extensive cybersecurity training has shown us that effective defense starts with attack surface reduction—making your business a harder target by closing unnecessary entry points and securing essential ones.
Vulnerability management is another cornerstone, requiring continuous scanning, assessment, and patching of software weaknesses before they can be exploited. What truly sets apart mature security IT solutions is the integration of threat intelligence, which provides insight into active cybercriminal tactics so you can prepare specific defenses.
Continuous monitoring, often through a 24/7 security operations center, ties it all together, ensuring threats are spotted and stopped before they can cause real damage. These proactive measures should also align with IT Security Policy Compliance requirements.
In today's world of remote work and cloud computing, the old model of a secure internal network is obsolete. Zero Trust architecture flips the script, operating on a simple principle: "Never trust, always verify." Every user, device, and application must prove their identity and authorization for every access request.
This is achieved through strict identity verification, the principle of least privilege (granting only necessary access), micro-segmentation to create internal network barriers, and multi-factor authentication for an added layer of protection. The results are significant: organizations using Zero Trust models can see up to a 90% reduction in successful data breaches. It's a fundamentally smarter approach to security. For a deeper understanding, learn more about Zero Trust principles.
Your digital "attack surface" includes all potential entry points cybercriminals could use. The first step is always asset findy—you cannot protect what you don't know exists. Our extensive cybersecurity training has taught us that businesses are often surprised by what we find, from forgotten servers to old user accounts.
Once assets are identified, risk prioritization is crucial. We help you focus on fixing the most critical vulnerabilities first. Patch management is also vital, as many major breaches exploit known issues for which patches were available. A disciplined approach to patching closes these obvious doors to attackers.
The businesses we work with in Columbus, Ohio and Charleston, WV often find that reducing their attack surface also simplifies their IT environment and reduces costs. Our approach includes Cybersecurity Audit and Compliance Solutions to ensure your efforts meet regulatory standards and strengthen your overall security.
As the cybersecurity battlefield evolves, traditional security measures are falling behind. Advanced technologies like Artificial Intelligence (AI) and Machine Learning (ML) are essential, acting as digital detectives that work 24/7 to protect your business.
At Next Level Technologies, our team's extensive cybersecurity training has shown us how these technologies are making security IT solutions fundamentally smarter. AI-powered threat detection analyzes millions of data points in seconds, while security automation frees up your IT team to focus on strategic initiatives. SOAR (Security Orchestration, Automation, and Response) platforms create a seamless defense system that responds to threats faster than any human could.

With AI expected to be used in 90% of cyberattacks by 2025, it's simple: if attackers are using AI, we must use AI to defend.
AI and ML are game-changers that make security IT solutions dramatically more effective:
This speed advantage means threats that once went unnoticed for weeks are now caught in minutes. Our clients in Columbus, Ohio and Charleston, WV have seen how manual investigation is replaced by automated, real-time protection.
Even the best security IT solutions can't guarantee 100% protection. Your recovery strategy is as critical as your prevention strategy. Our extensive cybersecurity training has taught us that a solid plan is essential for resilience.
For detailed guidance, see our insights on IT Security Incident Management. Our team works with businesses in Columbus, Ohio and Charleston, WV to ensure their recovery plans are tested, practical, and ready.

A staggering 95% of cybersecurity breaches are due to human error. This sobering truth shows that technology is only as strong as the people using it. After years of implementing security it solutions across Columbus, Ohio and Charleston, WV, our team has learned that humans can be your strongest defense—or your weakest link.
Building a cyber-resilient organization means creating a security culture where everyone understands their role in protecting the business. When employees know how to spot a phishing email or why they shouldn't use a random USB drive, they become active guardians of your digital assets.
This human-centered approach extends to your partners as well. Third-party risk and supply chain security are critical, as the security practices of your vendors and contractors directly impact your own.
For practical guidance on building this foundation, check out our 10 Cybersecurity Tips for Small Businesses.
Effective cybersecurity training empowers employees with the knowledge to recognize and avoid threats.
Our technical experience shows that well-trained employees can reduce security incidents by up to 70%. For more insights, explore our guide on 5 Common Cybersecurity Threats to Small Businesses and How Managed IT Services Can Help.
Cookie-cutter security it solutions often fail because different industries face unique risks. Our team's extensive cybersecurity training ensures we tailor defenses to your specific needs.
We also help clients steer key standards like GDPR and SOC 2. Our managed services division has achieved SOC 2 compliance, giving us experience in meeting these strict standards. Effective security it solutions must be customized to your industry's risks and regulations.
Business owners often ask us thoughtful questions about security IT solutions. Here are some of the most common concerns and how our team approaches them.
The first step is always a comprehensive risk assessment or security audit. This process identifies your critical assets, spots existing vulnerabilities in your systems and processes, and creates a prioritized roadmap for improvement. You can't fix what you don't know is broken.
Our team in Columbus, Ohio and Charleston, WV starts every client relationship with an audit, providing a clear picture of where you stand and actionable steps for improvement.
If your business handles sensitive data, has a remote or hybrid workforce, or uses cloud services, a Zero Trust model is highly beneficial. It's a modern approach that moves beyond outdated perimeter-based security to protect resources in today's distributed work environments.
Given that Zero Trust can reduce the likelihood of a data breach by up to 90%, our extensive cybersecurity training and technical experience lead us to recommend it for virtually any modern business.
Yes. Modern security IT solutions are scalable, and partnering with a Managed Security Service Provider (MSSP) like Next Level Technologies offers a cost-effective way to access enterprise-grade tools and expertise without the high cost of an in-house security team.
We specialize in offering comprehensive IT solutions that make world-class security accessible to businesses of all sizes. The real question isn't whether you can afford comprehensive security, but whether you can afford not to, especially when the average data breach cost $4.45 million in 2023.
As we've covered, modern cybersecurity is a complex, multi-faceted challenge. With the average data breach costing $4.45 million and 95% of breaches stemming from human error, the need for robust security IT solutions is undeniable.
For many businesses, navigating this landscape while keeping up with new threats and a growing cybersecurity skills gap feels overwhelming. That's where partnering with a dedicated expert like Next Level Technologies makes all the difference.
With over 20 years of experience and insights from 300+ security researchers and intelligence analysts, our team brings extensive cybersecurity training and deep technical experience to your business. We act as your outsourced IT security department—we manage your security posture, reduce your attack surface, and ensure compliance, so you can focus on growth.
Whether you're in Columbus, Ohio, or Charleston, WV, we are here to provide comprehensive managed IT services and support. We deliver cutting-edge security IT solutions designed for businesses of all sizes, ensuring top-tier protection is accessible to everyone.
Don't wait until a disaster strikes. As the saying goes, "Cyber attacks are just like a building fire. By the time you realize you need protection, it may be too late." Let us help you build a strong, resilient, and future-proof defense for your business.
Secure your business with expert Managed IT Services and Support
Discover how IT server management services boost uptime, security, and compliance for businesses in Columbus, Ohio and Charleston, West Virginia.
June 2, 2026
Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026
Next Level Technologies was founded to provide a better alternative to traditional computer repair and ‘break/fix’ services. Headquartered in Columbus, Ohio since 2009, the company has been helping it’s clients transform their organizations through smart, efficient, and surprisingly cost-effective IT solutions.
