Protecting Your Pennies: Secure File Sharing for Financial Firms
August 29, 2025

Discover how IT server management services boost uptime, security, and compliance for businesses in Columbus, Ohio and Charleston, West Virginia.
June 2, 2026

Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026

Strengthen your defenses with Vendor risk management services. Discover risks, compliance strategies, and lifecycle best practices now!
April 23, 2026
August 29, 2025
Secure file sharing finance solutions are essential as financial firms face mounting pressure from cybercriminals and regulators. When your business handles millions in daily transactions, a single data breach can destroy client trust and lead to devastating financial penalties.
Quick Answer for Financial Firms Seeking Secure Sharing:
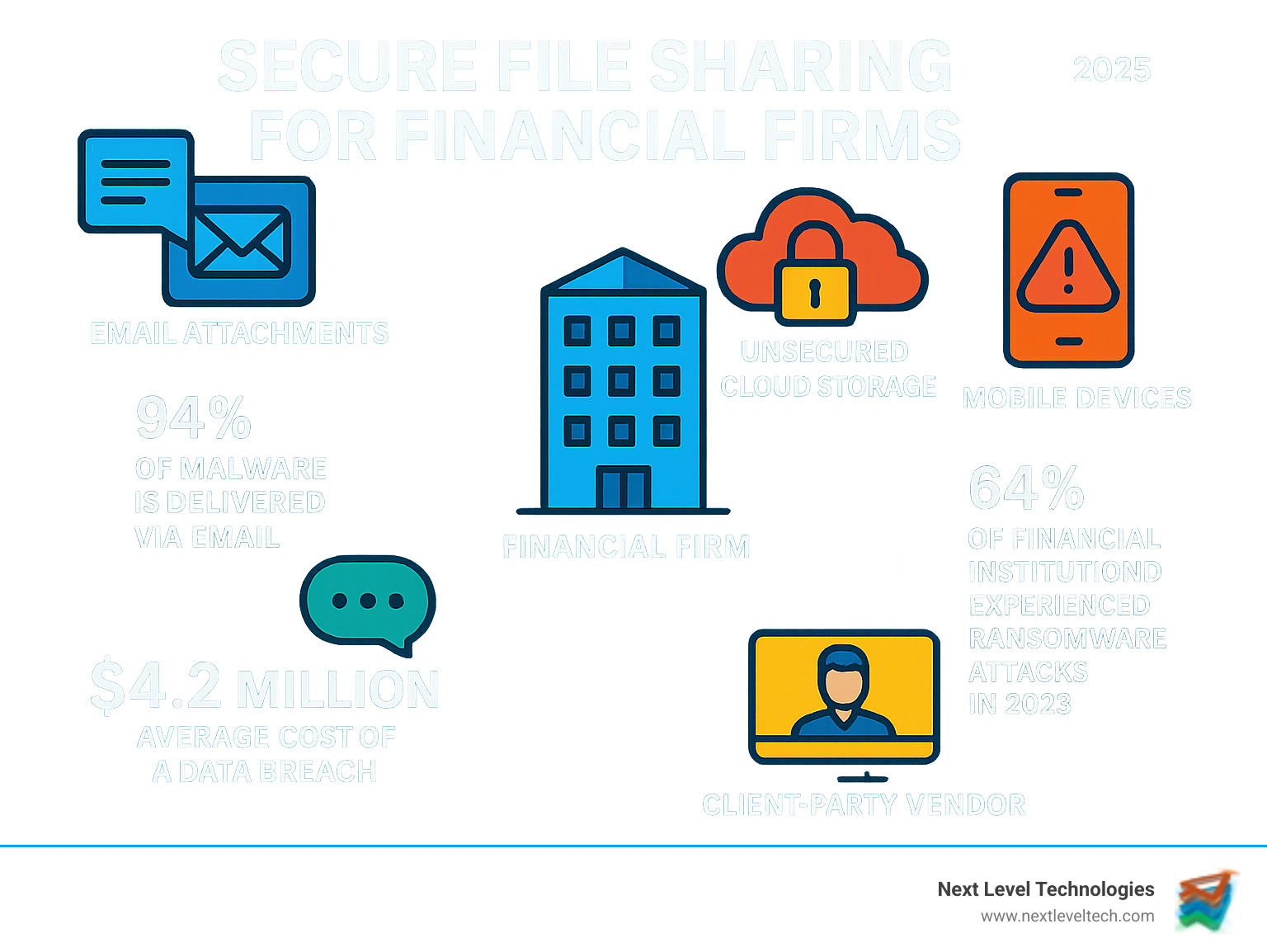
The stakes couldn't be higher. Since 94% of malware is delivered via email, traditional sharing methods are extremely risky. Meanwhile, ransomware attacks on financial institutions are on the rise. Incidents like the Capital One breach, which exposed over 100 million customer records, highlight why generic file sharing tools are insufficient for financial data.
Financial firms need purpose-built solutions that go beyond basic cloud storage. Your clients trust you with their most sensitive information—Social Security numbers, bank details, and investment portfolios. Every document must be protected with bank-level security.
The regulatory landscape adds another layer of complexity, with FINRA, GLBA, and SOX all setting specific requirements for data handling. Non-compliance is expensive, with average data breach costs reaching millions per incident.
I'm Steve Payerle, President of Next Level Technologies. For over 15 years, I've helped financial firms in Columbus, Ohio and Charleston, WV implement robust secure file sharing finance solutions. My team's extensive cybersecurity training has protected countless businesses from the growing threats targeting financial data, and I've seen how the right technology transforms both security and efficiency.
Explore more about secure file sharing finance:

Working in financial services means you're running a digital Fort Knox, handling information that cybercriminals are constantly trying to steal. The numbers are sobering: 64% of financial institutions experienced ransomware attacks in 2023, a significant increase from the previous year. These attacks can paralyze your entire operation overnight, locking critical systems and client files.
Data breaches are an even more insidious threat. The Capital One breach exposed over 100 million customer records due to a single misconfigured firewall, leading to massive fines and irreparable reputational damage. Phishing campaigns also pose a major risk, as cleverly disguised emails trick staff into compromising your entire network. The aftermath of these failures includes loss of client trust, steep financial penalties, and costly incident response efforts.
When we discuss secure file sharing finance, we're protecting a wide range of critical information. This includes:
If exposed, any piece of this data can lead to identity theft and financial fraud. Your clients' trust is your most valuable asset and greatest responsibility.
The regulatory landscape for financial data is complex, but each rule serves to protect clients and maintain market integrity.
These regulations are not just bureaucratic problems; they are a roadmap for protecting sensitive information. Our team's extensive cybersecurity training helps firms in Columbus, Ohio and Charleston, WV steer these requirements. Proper cybersecurity compliance services build a foundation of trust that becomes a competitive advantage.

A true secure file sharing finance solution is not just cloud storage with a password; it's a purpose-built fortress for your most sensitive data. Many firms make the mistake of using basic cloud tools to protect information worth millions.
A real financial platform is designed for the industry's unique challenges, protecting data both at rest (on servers) and in transit (while traveling). Every file is wrapped in multiple layers of security.
At Next Level Technologies, our team's extensive cybersecurity training has shown us what separates amateur solutions from professional-grade protection. Our IT Security for Banks approach ensures every component works together seamlessly.
How your data moves is critical. While HTTPS provides basic encryption for web browsing, financial data requires more robust protocols.
SFTP (Secure File Transfer Protocol) is the gold standard for moving sensitive data. It wraps both files and commands in SSH encryption, providing bulletproof protection for regulatory reports, transaction data, and client portfolios.
FTPS is outdated technology. Despite the "S," it struggles with modern firewalls and adds unnecessary complexity. Our cybersecurity-trained staff recommends avoiding it for new implementations.
Managed File Transfer (MFT) solutions go even further by automating the secure exchange of large data volumes while providing extensive audit capabilities and seamless integration with existing systems.
Several technologies make secure file sharing finance work effectively.
Secure cloud platforms must be designed specifically for financial services, with proper permission controls, data residency options, and built-in compliance features. Our expertise in Cloud Computing for Banks helps firms choose solutions that meet the strictest standards.
Virtual Data Rooms (VDRs) are the Fort Knox of file sharing, ideal for M&A and sensitive audits. They offer dynamic watermarking, view-only access, and detailed audit trails that log every interaction.
Secure web forms are game-changers for client onboarding, allowing you to collect sensitive information directly into your protected systems, encrypted from the moment of entry.
Avoid P2P (Peer-to-Peer) networks for financial data. Their decentralized nature eliminates central control, auditability, and the robust security required for compliance. The risks are simply not worth it.
For secure file sharing finance solutions, a single security measure is never enough. Our team at Next Level Technologies, with its extensive cybersecurity training, always recommends a layered approach for proactive defense and granular control. A truly secure platform integrates multiple features to create an environment where staff can work efficiently and securely. Our Cybersecurity Services are built on this principle of comprehensive protection.
Encryption turns readable information into a secret code. For financial data, AES 256-bit encryption is the standard, used by government agencies and major banks. End-to-end encryption is critical, as it protects data on your device, during transit, and until it reaches the recipient. Even if intercepted, the data is unreadable. Some platforms offer zero-knowledge encryption, meaning not even the service provider can access your data.
Multi-factor authentication (MFA) adds another layer of security. It requires multiple forms of verification, such as a password (something you know) and a code from your phone (something you have). This dramatically reduces the risk of unauthorized access, even with a compromised password, making MFA essential for any financial firm.
Giving everyone access to everything is a major security risk. Role-based access control (RBAC) ensures users can only access data relevant to their jobs. For example, financial analysts can see client portfolios but not HR records. You can get even more specific with folder-level permissions and user-specific access to control who can view, edit, download, or share each document.
Advanced features like printing controls and download restrictions prevent internal data leaks. They allow users to view sensitive documents in a secure environment without being able to print them or save them to unsecured devices, which is especially useful when working with third parties.
In finance, accountability is a legal requirement. Comprehensive audit logs track every file interaction: who accessed what, when, from where, and what they did. This is invaluable for compliance, security, and internal investigations. Modern systems also use anomaly detection to automatically flag suspicious activity, like a user downloading an unusual number of files, and send alerts before a breach occurs.
Dynamic watermarking adds another layer of accountability by overlaying documents with the viewer's name, timestamp, or IP address. This deters leaks and helps trace the source if a document is ever exposed. These features, combined with robust Data Backup and Recovery strategies, form the backbone of a secure financial file sharing environment.

Beyond security, the best secure file sharing finance solutions transform your firm's operations and build client trust. With most financial institutions increasing technology spending, smart firms are choosing platforms that deliver both security and efficiency. At Next Level Technologies, our team's extensive cybersecurity training has helped firms in Columbus, Ohio and Charleston, WV adopt solutions that clients enjoy using. Our IT Support for Financial Services focuses on this balance.
Many firms juggle multiple systems, creating inefficiency and security gaps. The solution is a purpose-built secure file sharing finance platform that offers:
By moving sensitive file sharing away from email, you dramatically reduce clutter and the associated security risks.
Remote work requires clear remote access policies that define approved devices and security protocols. Endpoint security is critical, ensuring every device accessing your data is protected with antivirus, anti-malware, and regular updates. Our team's extensive cybersecurity training helps firms implement these controls seamlessly.
Modern platforms often provide VPN alternatives based on zero-trust principles, verifying every access request regardless of location. The key is maintaining a consistent security posture whether your team is in the office or working remotely. Our Cloud Security Best Practices guide helps firms achieve this.
In finance, trust is everything. Secure platforms build it in powerful ways:
The client experience improves dramatically with streamlined, secure sharing. When you get secure file sharing finance right, security becomes invisible to clients while remaining impenetrable to threats.
Secure file sharing finance platforms are essential for meeting regulatory requirements. They provide auditable proof of data handling by creating an immutable record of every file access, change, or download. When auditors arrive, you have a complete trail demonstrating compliance. These platforms also enforce automatic access controls through features like MFA and role-based permissions, ensuring only authorized users can see sensitive data, as required by GDPR and PCI-DSS. Finally, data encryption for data at rest and in transit is a core feature, meeting another key compliance cornerstone. They can also help automate data retention policies to meet various legal requirements.
Comparing general cloud storage to a specialized secure file sharing finance solution is like comparing a bicycle to an armored car. General services are built for convenience and lack the granular security and compliance features needed for financial data. Specialized financial solutions are built from the ground up for security. Key differentiators include:
Security is a core component of financial solutions, not an add-on.
While no technology is 100% foolproof, secure file sharing finance solutions dramatically reduce your risk of a data breach. They work by:
In my experience, the right platform turns a potential disaster into a manageable event by creating multiple layers of protection that are difficult to penetrate.
The financial world has changed, and secure file sharing finance is now a business necessity. The right technology transforms your firm, allowing you to confidently serve clients while staying ahead of threats. A single breach can destroy decades of trust, but a robust solution creates a competitive advantage that builds client confidence.
We've covered how key features work together:
Adopting a proactive approach to security puts you in control, neutralizing risks before they can cause damage. This shift from reactive patching to proactive protection is what separates thriving financial firms from those struggling with security incidents.
This is where expert guidance is invaluable. At Next Level Technologies, we have spent over 15 years helping financial firms steer these challenges. Our team brings extensive cybersecurity training and deep technical experience custom to financial services. We understand that firms in Columbus, Ohio, and Charleston, West Virginia, face sophisticated threats and need solutions that fit their scale.
We don't just implement technology; we become your trusted partner. Our managed IT services approach means we monitor your systems 24/7, ensuring your secure file sharing finance solutions evolve with threats and regulations. You can focus on helping clients achieve their goals while we handle the complexities of cybersecurity.
Ready to transform your firm's security and efficiency? Get expert IT support for your financial firm and find how the right partnership can secure your success.
Discover how IT server management services boost uptime, security, and compliance for businesses in Columbus, Ohio and Charleston, West Virginia.
June 2, 2026
Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026
Next Level Technologies was founded to provide a better alternative to traditional computer repair and ‘break/fix’ services. Headquartered in Columbus, Ohio since 2009, the company has been helping it’s clients transform their organizations through smart, efficient, and surprisingly cost-effective IT solutions.
