Vendor Risk Management: Securing Your Business Ecosystem
March 21, 2026

Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026

Strengthen your defenses with Vendor risk management services. Discover risks, compliance strategies, and lifecycle best practices now!
April 23, 2026

Discover top cloud management app tools for 2025. Optimize multi-cloud, boost security, cut costs & master hybrid environments like a pro!
April 17, 2026
March 21, 2026
Vendor Risk Management is the process of identifying, assessing, and mitigating risks that third-party vendors introduce to your organization — across cybersecurity, compliance, operations, and more.
Here's a quick breakdown of what effective Vendor Risk Management involves:
Most businesses focus heavily on their own internal security. But here's the problem: your vendors can bypass all of it.
Over 60% of data breaches now involve third-party vendors. The 2013 Target breach — triggered by a single vendor's compromised credentials — cost Target over $162 million and wiped out more than $400 million in market value. More recently, the Change Healthcare cyberattack exposed the data of 190 million Americans, making it the largest healthcare data breach in U.S. history.
These weren't failures of internal security. They were failures of Vendor Risk Management.
If your business relies on outside vendors — for software, payroll, cloud hosting, or anything else — you have third-party risk. The question is whether you're managing it or ignoring it.
I'm Steve Payerle, President of Next Level Technologies, and I've spent over 15 years helping small and mid-sized businesses across Columbus, Ohio and Charleston, WV build resilient IT environments — including implementing Vendor Risk Management strategies that protect against the growing wave of third-party cyber threats. In this guide, I'll walk you through exactly how to build a VRM program that actually works for your business.

Key terms for Vendor Risk Management:
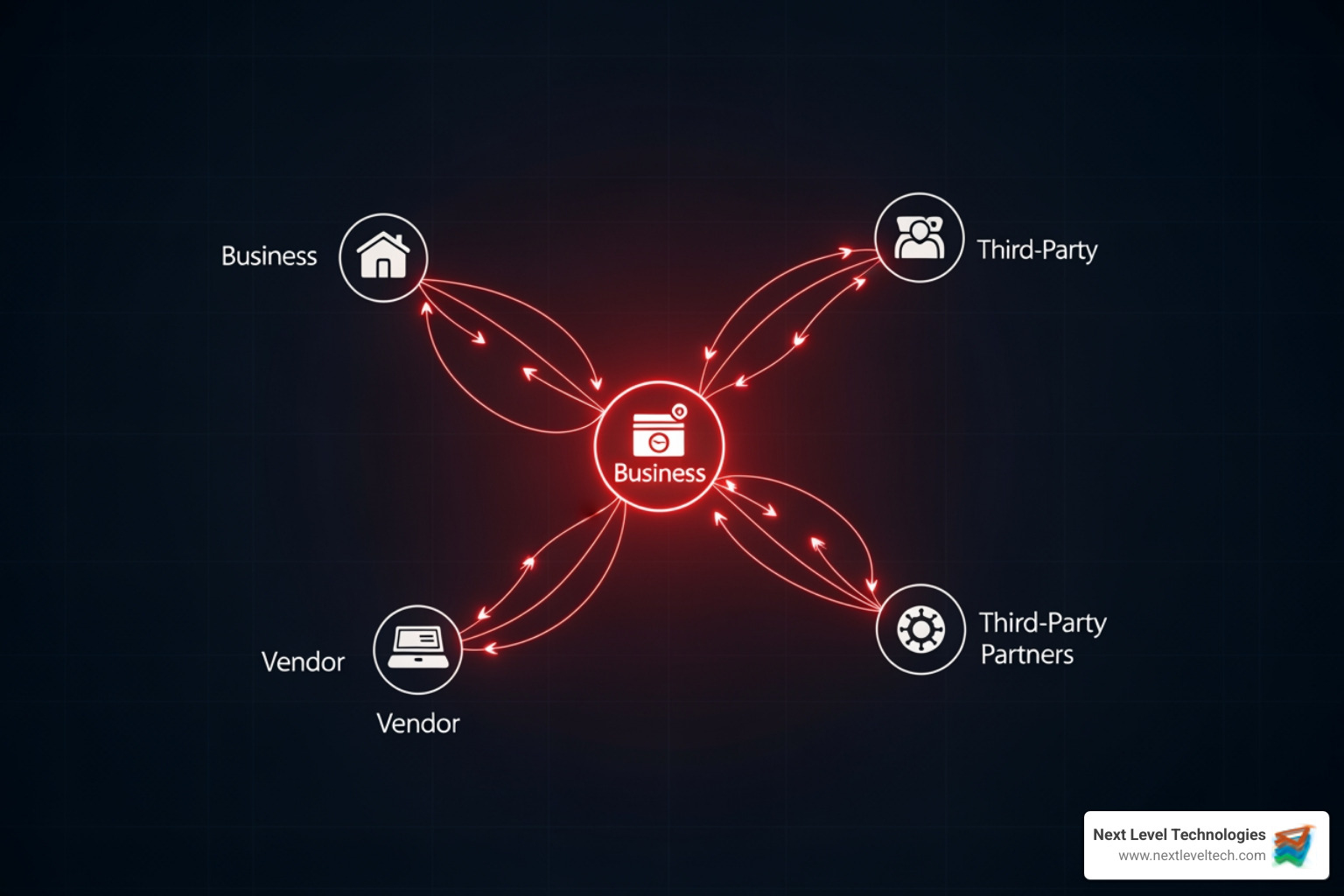
In our interconnected world, no business is an island. We rely on cloud providers for storage, SaaS platforms for CRM, and specialized contractors for everything from payroll to HVAC maintenance. While this helps us scale, it creates a massive "attack surface."
According to recent industry data, 30% of data breaches are now the result of third-party compromises. In fact, 54% of surveyed companies reported experiencing a breach due to a third party in 2023 alone. When a vendor fails, the fallout lands squarely on your doorstep.
Consider these high-stakes examples:
At Next Level Technologies, we see this often in the Midwest. Whether you're a medical clinic in Charleston, WV or a manufacturing firm in Columbus, OH, your reputation depends on the security of the people you do business with. Effective Vendor Risk Management isn't just about checking a box; it's about financial loss prevention and ensuring your doors stay open.
Managing vendor risk isn't a one-time event—it’s a continuous cycle. To protect your business, you need a structured vendor lifecycle approach that covers every interaction from the first handshake to the final goodbye.
Before you sign a contract, you must identify exactly what the vendor will do and what data they will access. We recommend identifying third-party vendors by looking across all departments, not just IT. Often, marketing or HR will sign up for a tool that the IT team doesn't even know exists!
Onboarding vendors is the most critical stage for setting expectations. This is where you conduct vendor due diligence procedures to verify their financial stability, performance, and cybersecurity posture. You should ask for inherent risks assessments to understand the baseline danger they pose.
A vendor that was secure last year might not be secure today. Continuous vendor risk monitoring involves using external cybersecurity and business risk intelligence to watch for new vulnerabilities, data leaks, or financial trouble in real-time.
This is where most companies fail. Research shows that 60% of companies are not actively assessing third-party risks during offboarding. A secure vendor offboarding approach must include revoking all contracts and access, followed by a formal data destruction verification.
To run a successful program, you need a dedicated it-vendor-management-analyst or a partner like us to oversee the moving parts. Key components include:
If you are still using spreadsheets to track 50 different vendors, you are fighting a losing battle. Modern it-vendor-risk-management-solutions use automation to make the process scalable and efficient.
FeatureManual SpreadsheetsAutomated VRM PlatformsData AccuracyHigh risk of human errorReal-time, verified dataScalabilityDifficult to manage >10 vendorsCan handle hundreds of vendorsAlertingNone (requires manual check)Instant real-time alertsReportingTime-consuming to buildOne-click executive dashboardsEfficiencyVery low (chasing emails)High (automated workflows)
By using centralized dashboards and real-time alerts, we help businesses in Columbus and Charleston gain efficiency and oversight without hiring a massive internal team.
When we talk to our clients about how-to-manage-it-vendors, we emphasize that you have to look beyond the surface. It’s not just about the vendor you hired; it’s about their vendors too.
Fourth-party risk is the risk introduced by your vendor's subcontractors. If your payroll provider uses a third-party cloud host that gets breached, your data is still gone. You must include requirements in your contracts that force your vendors to manage their own cyber risks effectively.
The world is a messy place. Russia’s invasion of Ukraine taught many businesses that geopolitical instability can instantly sever a supply chain or introduce state-sponsored cyber risks. Furthermore, ESG regulations are becoming more strict, meaning you could face legal trouble if your vendors engage in unethical environmental or social practices.
A Software Bill of Materials (SBOM) is essentially an "ingredient list" for software. By demanding an SBOM, you can see exactly what code components your vendor is using. This allows you to quickly identify if a newly discovered vulnerability (like Log4j) affects your business through a specific vendor.
Depending on your industry, Vendor Risk Management isn't just a good idea—it's the law. Regulators are increasingly holding businesses accountable for the actions of their partners.
Ensuring audit readiness means having a paper trail for every vendor assessment you've ever conducted. We help our clients build these "compliance-first" programs from the ground up.
In Vendor Risk Management, "third party" is the overarching term. It includes vendors (who sell products), suppliers (who provide raw materials), and service providers (who perform tasks). All vendors are third parties, but not all third parties are vendors.
For your most critical "Tier 1" vendors, we recommend continuous vendor risk monitoring. For lower-risk vendors, an annual assessment is usually sufficient. However, any major change—like a merger, a significant infrastructure shift, or a reported breach—should trigger an immediate reassessment.
Legally, you are. The law generally holds the client company responsible for protecting their customers' personally identifiable information (PII). While you might be able to sue your vendor for damages if your contracts are strong, the regulatory fines and reputational damage will fall on you.
Building a resilient business ecosystem requires more than just locking your own front door. It requires making sure your partners aren't leaving the back door wide open. From the initial onboarding vendors stage to the final secure offboarding, Vendor Risk Management is a full-time job.
At Next Level Technologies, we specialize in taking this burden off your shoulders. With locations in Columbus, OH, Worthington, OH, and Charleston, WV, our team brings extensive cybersecurity training and technical experience to the table. We don't just give you a piece of software; we provide the expert advisory services needed to navigate complex regulatory requirements and evolving cyber risks.
Don't wait for a vendor breach to cost you millions. Secure your business with managed IT support and let us help you build a proactive, automated, and secure vendor ecosystem today.
Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026
Strengthen your defenses with Vendor risk management services. Discover risks, compliance strategies, and lifecycle best practices now!
April 23, 2026
Next Level Technologies was founded to provide a better alternative to traditional computer repair and ‘break/fix’ services. Headquartered in Columbus, Ohio since 2009, the company has been helping it’s clients transform their organizations through smart, efficient, and surprisingly cost-effective IT solutions.
