The Ultimate Guide to IT Service Continuity Management
March 9, 2026

Master the basics of computer hardware and networking with this in-depth guide covering components, systems, and troubleshooting.
June 6, 2026

Discover how IT server management services boost uptime, security, and compliance for businesses in Columbus, Ohio and Charleston, West Virginia.
June 2, 2026

Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026
March 9, 2026
IT service continuity management ensures critical IT services continue or recover quickly during a disaster. Whether it's a cyberattack or system failure, ITSCM protects your business from extended downtime that threatens survival.
Quick Answer: What is IT Service Continuity Management?
Statistics show over half of SMBs close within six months of a cyber-attack. Every moment of downtime means lost revenue and damaged reputation. While routine issues go to the help desk, ITSCM handles worst-case scenarios like ransomware or physical destruction of server rooms.
I'm Steve Payerle, President of Next Level Technologies. With 15+ years helping businesses in Columbus, Ohio and Charleston, WV, I've seen how ITSCM makes the difference between survival and closure. Our team's extensive cybersecurity training and technical experience allow us to build resilient infrastructures that protect against the unexpected.
Quick it service continuity management definitions:
IT service continuity management (ITSCM) is a strategic framework ensuring IT services withstand and recover from disruptive events. It is the ultimate "what if" plan for your infrastructure, focusing on catastrophic scenarios like regional power outages or massive cyberattacks.
The ITIL® 4 framework recognizes ITSCM as a crucial practice for maintaining core activities and credibility. It combines proactive measures like redundancy with reactive recovery strategies. Achieving the industry standard 99.99% uptime requires this level of technical continuity.
FeatureIncident ManagementITSCMBCMFocusRapid restoration of normal serviceIT availability during disastersEssential business functionsScopeDay-to-day IT issuesMajor IT disastersAll business disruptionsGoalRestore service ASAPMeet RTO/RPO during disasterEnsure business survivalRelationshipHandles routine disruptionsIT-specific arm of BCMOverarching strategy
Incident Management is reactive, focusing on everyday problems. ITSCM is both proactive and reactive, planning for disasters that incident management cannot handle. Business Continuity Management (BCM) is the broader strategy ensuring the entire business operates during any disruption. ITSCM provides the IT-specific answers to the BCM strategy.
Building a robust strategy requires systematic preparation beyond simple backups.
A BIA identifies critical processes and quantifies the cost of disruption. It helps determine Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO). By identifying interdependencies, we prioritize restoring the most critical services first for our clients in Columbus and Charleston.
We evaluate threats in a VUCA world. Our assessment includes:
AWS provides guidance on setting these targets per application. We translate your resource usage data into concrete infrastructure requirements.
Following BCI Good Practice Guidelines, we use several models:
Our technical experience allows us to design the most appropriate model for your specific regional needs.
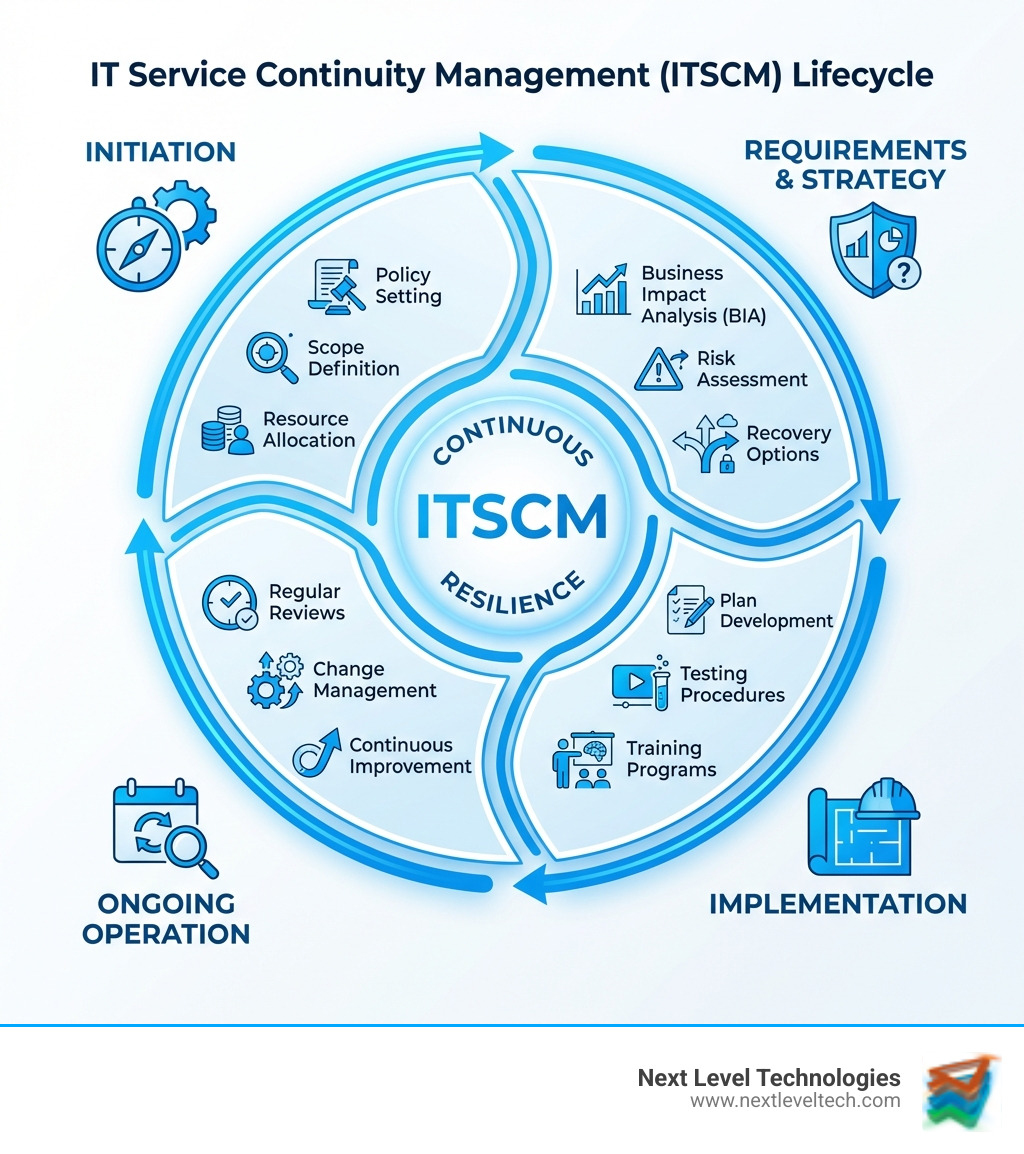
ITSCM is a cyclical journey involving four stages:
The plan must be specific and flexible, as per ISO 22301. It includes:
Plans must be tested to ensure they work. Our protocols include:
We recommend annual reviews or updates following significant infrastructure changes. Lessons learned are fed back into the plan, ensuring your strategy evolves with your environment.
Effective ITSCM requires clear leadership and defined roles.
Expert guidance helps steer these complexities for businesses in Columbus, Ohio and Charleston, WV, ensuring a robust defense against disruption.
IT service continuity management is absolutely critical for small and medium-sized businesses (SMBs). Statistics indicate that over half of all small and medium-sized businesses (SMBs) close within six months of experiencing a cyber-attack. Without an ITSCM plan, an SMB faces:
For SMBs in Columbus, Ohio and Charleston, WV, having a robust ITSCM plan is not a luxury; it's a necessity for safeguarding their future.
We recommend that IT service continuity management plans be tested at least annually. However, testing should also occur whenever there are significant changes to your:
Regular testing identifies weaknesses, ensures the plan remains relevant, and keeps recovery teams proficient.
Recovery Time Objective (RTO) is the maximum acceptable amount of time your IT services can be down after a disruption. It's about how quickly you need to restore functionality. For example, if your RTO is 4 hours, your critical systems must be back online within 4 hours of an outage.
Recovery Point Objective (RPO) is the maximum acceptable amount of data loss you can sustain. It's about how much data you can afford to lose. If your RPO is 1 hour, your backup strategy must ensure you can recover all data up to an hour before the disruption.
In simple terms, RTO is about time to recover, and RPO is about how much data you lose. Both are crucial in defining your IT service continuity management strategy.
In an unpredictable world where digital systems are the lifeblood of business, robust IT service continuity management is no longer optional—it's foundational to survival and success. From comprehensive Business Impact Analysis and proactive Risk Assessments to meticulous recovery planning and rigorous testing, each component plays a vital role in building resilience.
We've explored why ITSCM is critical, how it differs from other IT processes, its core components, and the steps involved in implementation. We've also highlighted the importance of clear roles, continuous improvement, and addressing common challenges to ensure your business is prepared for anything.
At Next Level Technologies, we understand the unique IT landscapes of businesses in Columbus, Ohio and Charleston, WV. Our team's extensive cybersecurity training and deep technical experience mean we're not just providing managed IT services; we're building a fortress of continuity around your operations. We partner with you to develop custom ITSCM strategies that align with your business goals, minimize downtime, and protect your bottom line. With Next Level Technologies, you gain a partner dedicated to ensuring your IT services are always ready for what comes next.
Ready to secure your business's future against unforeseen disruptions? Learn more about our comprehensive Managed IT Services and Support.
Master the basics of computer hardware and networking with this in-depth guide covering components, systems, and troubleshooting.
June 6, 2026
Discover how IT server management services boost uptime, security, and compliance for businesses in Columbus, Ohio and Charleston, West Virginia.
June 2, 2026
Next Level Technologies was founded to provide a better alternative to traditional computer repair and ‘break/fix’ services. Headquartered in Columbus, Ohio since 2009, the company has been helping it’s clients transform their organizations through smart, efficient, and surprisingly cost-effective IT solutions.
