The IT Security Assessment Playbook: What You Need to Know
March 10, 2026

Master the basics of computer hardware and networking with this in-depth guide covering components, systems, and troubleshooting.
June 6, 2026

Discover how IT server management services boost uptime, security, and compliance for businesses in Columbus, Ohio and Charleston, West Virginia.
June 2, 2026

Discover top IT consulting Columbus Ohio firms. Explore services, cybersecurity, costs & why local expertise drives business growth.
April 25, 2026
March 10, 2026
IT security assessment services help businesses identify vulnerabilities, evaluate security controls, and build defenses against cyber threats before attackers can exploit them. Here's what you need to know:
Quick Answer: What IT Security Assessment Services Do
The numbers tell a sobering story. Cybercrime will cost the global economy $10.5 trillion annually by 2025. Even more alarming: 71% of data breaches happen to small businesses, and nearly half of all small businesses have already been victims of cyberattacks. These aren't just statistics—they represent real companies that lost customer trust, revenue, and sometimes their entire business because they didn't know where their security gaps were.
Every slow network, every glitchy system, every security concern is trying to tell you something. Your technology has a story, and an IT security assessment helps you listen before that story becomes a crisis.
Think of an IT security assessment as a comprehensive health checkup for your digital infrastructure. Just as you wouldn't wait until you're seriously ill to see a doctor, you shouldn't wait for a breach to evaluate your security posture. These assessments examine everything from your network architecture and cloud services to how your employees handle phishing attempts and whether your backup systems would actually work in a disaster.
As Steve Payerle, President of Next Level Technologies, I've guided businesses in Columbus, Ohio and Charleston, WV through comprehensive IT security assessment services since 2009, helping them transform from reactive firefighting to proactive defense. Our team's extensive cybersecurity training and technical experience have shown us that businesses don't fail because they lack technology—they fail because they don't understand their vulnerabilities until it's too late.
Terms related to it security assessment services:

When we talk about IT security assessment services, we aren't just talking about running a quick scan and calling it a day. We’re talking about a deep-dive evaluation of your entire digital ecosystem. This "digital health check" is the foundation of a proactive defense. In the past, many businesses in the Columbus and Charleston areas could get away with being reactive—fixing things only when they broke. Today, that approach is a recipe for disaster.
Why is this so critical? Because StaySafeOnline.org reports that 71% of data breaches happen to small businesses, often because these organizations assume they are too small to be a target. In reality, hackers see smaller businesses as "soft targets" with fewer defenses.
A proper assessment serves several vital functions:
In short, an assessment gives you the visibility needed to allocate your budget where it matters most, rather than guessing which "shiny new tool" might save you.
A comprehensive assessment doesn't leave any stone unturned. We look at the digital, the physical, and the human elements of your organization.
To better understand the tools we use, it’s helpful to compare the two "heavy hitters" of the assessment world:
FeatureVulnerability AssessmentPenetration TestGoalIdentify and list all known weaknesses.Exploit weaknesses to see how far an attacker can get.ApproachSystematic and comprehensive.Targeted and goal-oriented.FrequencyMonthly or Quarterly (Automated).Annual or after major changes (Manual).OutcomeA prioritized list of vulnerabilities.Proof of how a breach could occur.
We often use NIST standards for security assessments to guide our framework, ensuring that our methods are backed by the highest level of federal and industry-standard rigor. This includes specialized focus on cloud environments (like Microsoft 365) and the growing world of IoT devices, which often lack built-in security.
To get the most accurate picture of your security, we employ several advanced methodologies:
The world of IT security doesn't stand still, and neither do we. Some of the biggest shifts we’re seeing include:
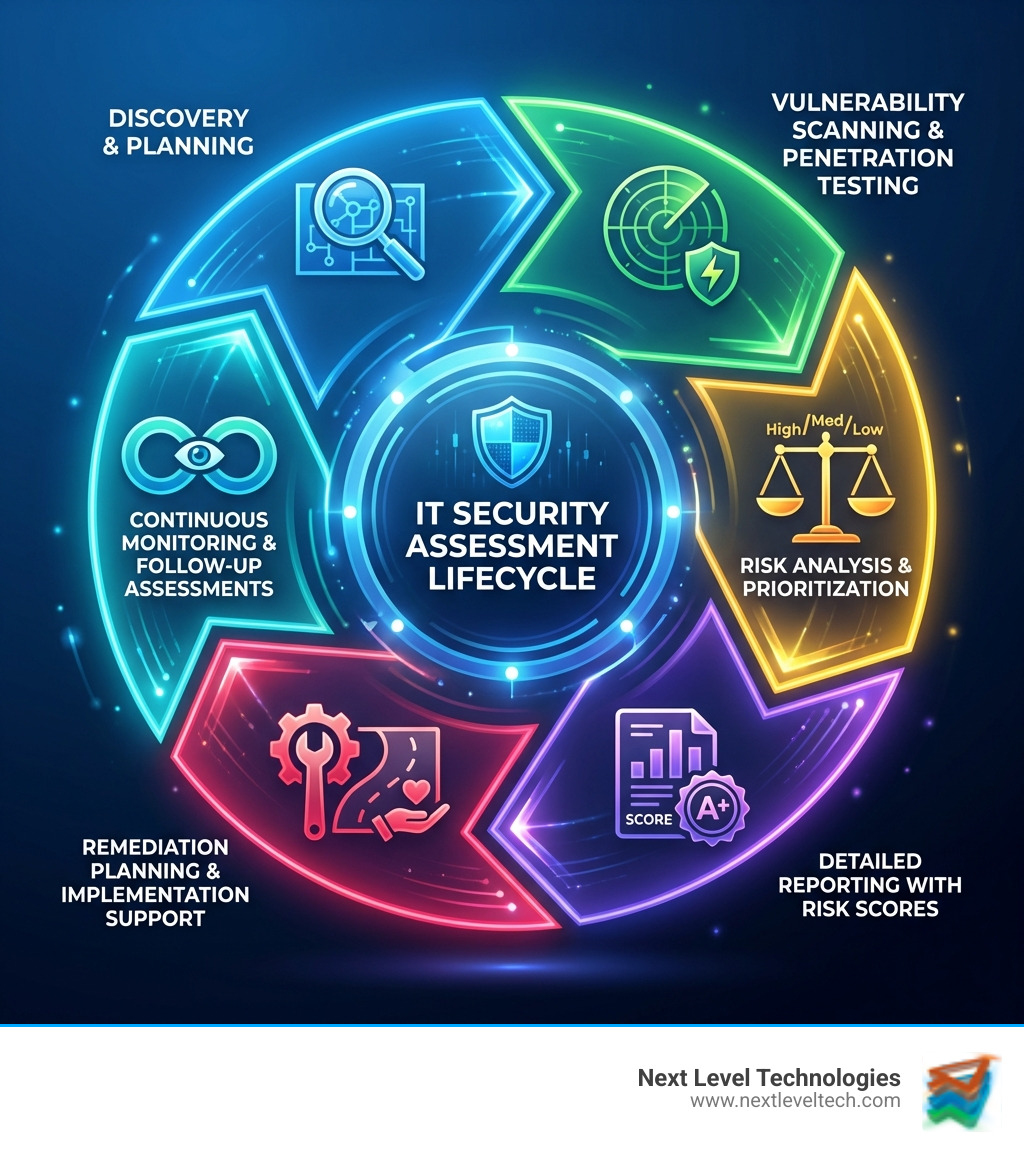
We believe in a transparent, step-by-step process. You should never feel like you're just getting a "black box" report.
For many of our clients in Ohio and West Virginia, IT security assessment services aren't just a good idea—they are a legal requirement. Whether you are a healthcare provider in Columbus or a defense contractor in Charleston, compliance is key to your survival.
Achieving compliance does more than just avoid fines; it builds massive customer trust and provides a legal "safe harbor" in the event of a dispute.
Choosing a partner for IT security assessment services is a big decision. You need someone who understands the local landscape in Columbus, Worthington, and Charleston. At Next Level Technologies, we pride ourselves on:
We provide unbiased, third-party reporting. Sometimes, an internal IT team is too close to the project to see the flaws. We provide that "fresh set of eyes" to ensure nothing is missed.
At a minimum, you should have a comprehensive assessment once a year. However, we recommend quarterly vulnerability scans and immediate assessments after any major change to your network, such as moving to the cloud or opening a new office location.
Think of a vulnerability assessment as someone walking around your house checking if any windows are open uped. A penetration test is that same person actually trying to climb through the window to see if they can get to your safe. One identifies the "hole," the other proves the "risk."
You should expect a comprehensive package including:
Your security posture is the only thing standing between your business and a $10.5 trillion global crime wave. By investing in proactive IT security assessment services, you aren't just "buying insurance"—you are building immunity.
At Next Level Technologies, our technical staff's experience and extensive cybersecurity training are at your disposal. Whether you are in Columbus, OH or Charleston, WV, we are here to help you optimize your resources and close the gaps before a hacker finds them.
Don't let your business become another statistic. Secure your business with managed IT services and support from a team that knows how to turn your vulnerabilities into strengths. Give us a call today, and let’s start writing a better story for your technology.
Master the basics of computer hardware and networking with this in-depth guide covering components, systems, and troubleshooting.
June 6, 2026
Discover how IT server management services boost uptime, security, and compliance for businesses in Columbus, Ohio and Charleston, West Virginia.
June 2, 2026
Next Level Technologies was founded to provide a better alternative to traditional computer repair and ‘break/fix’ services. Headquartered in Columbus, Ohio since 2009, the company has been helping it’s clients transform their organizations through smart, efficient, and surprisingly cost-effective IT solutions.
